ClevGuard Support: Monitor Devices with Others' Permission.
You are connected to digital world through phone number. Your mobile phone number especially follows you everywhere. You use your phone number to access membership benefits at shop, to communicate with bank and share family pictures.
When your number gets into the wrong hands,it can be very vulnerable.
What can someone do with your phone number? They may use your phone number to create complete digital profile of you, for scamming purpose because track someone by phone number is easy for hackers.
- 1. What Can A Stranger Do With Your Number?
- 2. How to Protect Your Phone Number From Being Abused?
- 3. How Do Hackers Get Your Phone Number
- 4. Summary
What Can A Stranger Do With Your Number?
Strangers or Scammers use your phone number to steal your identity and take over almost every online account you have. Hacker uses People search sites that reveals your personal information like your phone number,address, bankruptcies, past records, and family member’s names etc. Just for the sake of blackmailing stalking or identity theft.
Tracking your location
Track someone by phone number is quite easy. Hacker gain access to the SS7 system, they can track a person’s location based on cell phone number mast triangulation, read their sent and received text messages,and log, record and listen into their phone calls.
The mobile network and small GPS chip are independently work so if hacker take over mobile number it knows where you are. Because he hit targeting the mobile network. Which is not controlled by any customer.
Phone Scams and Frauds
What can a scammer do with my cell phone number? Hackers do scams and frauds by tracking someone's phone number.They try to steal your money or personal information through phone number. Hackers reach you by phone calls from real people, robocalls, or text messages.
They try to hijack your bank account using your cell phone number or phone number. Lottery scammers use your phone number to claim that you’ve won a prize and ask you for money or personal information through fake lotteries.
Steal Your Identities
Can someone steal your identity with your phone number? Sure, scammers use your cell phone number to take control of your online identity-your social media accounts and bank accounts, emails and text messages.
In many cases you receive a bill for a new mobile phone that you did not order.The scammers used your personal information to open a new account. Your phone stops working completely because a scammer used your information to upgrade to a new phone and your phone maybe shut off.
Access Your Social Media Accounts
If hacker can hack someone’s phone with just their numbers, then it's very easy for him to gain access on your online accounts. The number one thing hacker's do. He had set up a fake profile, along with a single photo and acopy of a recent post, and started to conversation to his friends.
The first way scammers access social media accounts is using re-used passwords, matter how strong and secure your social media passwords. Your accounts can still be in danger.
It's very clear, if you've shared your password with others, your account is not completely secure.Phishing
Phishing is another very popular method of social media accounts hacking, when hackers giving up your account details or information using deception. Send a "lure", a message, fake website or email make you panic you and need you to change your password urgently.

How to protect your Phone Number From Being Abused?
Be caution about sharing your information
Hacking someone's phone with just their number is quite common now a days so be careful while sharing your personal information online, such as your address, phone number especially because tracking someone by phone number is game of fun for hackers, family members’ names, car information, work history and bank account information is put you at severe risk.
Avoid embedding the GPS Coordinates in the photo, capture from smartphones scammers can know the location of where the picture was taken and easily find you.
Don’t click unsecured emails or links
Do not open emails from unknown people or sources, especially when they are unsolicited. Clicking on links or downloading attachments may contain viruses and infect your computer or subject you to fraud. Some links or attachments have the ability to steal your personal information and ultimately your identity.
Secure your smartphone
For casual phone users, please change your phone’s default passcode. Use complex code, rather "1234", "0000" and “2580” codes that are commonly used.
Don't use unprotected Bluetooth networks and turn off your Bluetooth service when you aren’t using it. Avoid using public WIFI. Hacker keep their eyes on important locations, if you use your bank accounts via public WIFI they can easily steel your money. Regularly delete your browsing history, cookies, and cache.
Two-factor authentication
There are different types of two step authentication. Commonly sent a single-use code as an SMS message to your phone number, which you then enter following a prompt from the website or service you’re trying to access. This method is familiar among social media users. it seems safe enough, and keep your online account secure.
Hackers know how to transfer a victim’s phone number to their own phone and so they can easily access their online accounts. This is known as SIM swapping. You should enable two step authentications on all your online account. Never ever share your phone number to strangers.
Get ClevGuard real-time protection
ClevGuard as a spyware detection app which can filter out malicious files and undetectable spyware on your phone. It makes your internet surfing safe.
You can use ClevGuard to scan unsafe phone app and set notification reminder with unsecure App. It Scan Phone files and separate them to the whitelist or Blacklist.
Help in scanning all third-party applications installed on your phone. Reporting all app access permission according to the risk grade. ClevGuard is professional in 24/7 heuristic scanning phone’s download files and report the abnormal documents.
How To Use ClevGuard Security Tool?
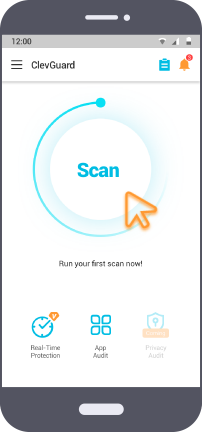
Step 1: Press Get in on Google Play button to download and install ClevGuard.
Step 2: Open ClevGuard anti-spyware, click "Scan" button it will quickly scan and detect spyware that has been installed on your smartphone.
Step 3: When scanning complete, you can checkout results and remove spyware instantly by click "Fix".
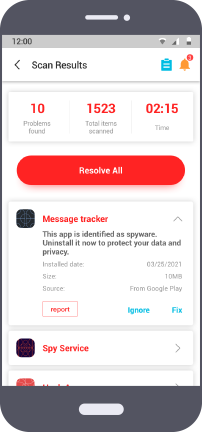
If there exist no spyware or malware on your mobile phone, you don't need to "Fix"."Report" is used under uncertain application security conditions. For certain security software, you can select "ignore".
Main Features of Anti-spyware ClevGuard
Detect and remove spyware in one click
Firstly, install ClevGuard, it run and scan spyware on your phone if found and suspicious activity it will display in front of you. It will monitor your phone in real-time to detect any traces of harmful spyware and remove it immediately.
ClevGuard mobile app security audit
ClevGuard will scan every app on your phone in a very deep. When auditing is complete, it will show you results,including app permissions, overlays, background usage,etc.
Scan all phone apps and files
ClevGuard is built on advanced technology,it performs a rapid scan of all third-party apps to see whether there are harmful or malicious for your phone.
How Do Hackers Get Your Phone Number?
Can someone steal your identity with your phone number? Yes, beacuse it's very easy to hack someone’s phone with just their number.
So, at most of cases hackers find the phone number of their target from internet or from a phone bill. Then call up carrier impersonating the customer,and, cleverly answered the questions like where a person lives or their date of birth, and ask the customer service representative to port out your phone number to another mobile phone's SIM card.
When "port out" completes, the phone number activates on hacker's SIM card,and the hacker can send and receive messages and make calls.
Summary
Phone number tracker are very smart nowadays they can track someone by mobile phone number and continuously create spyware and malicious software to steal our privacy and sensitive information secretly. If you don't have any idea about system technology, then you are unaware if the spyware is hidden in your phone. In this field, ClevGuard would be strongly recommended to use, it is completely safe and secure. It could give you details information about malicious app and files on your phone in few seconds as soon as scanning is completed. Providing 24 hours protection of mobile phone.







