ClevGuard Support: Monitor Devices with Others' Permission.
Is remote computer hacking possible? How can I successfully hack someone's computer in a legal way?
While you may think that hacking into a computer from another device may be nearly impossible, it is indeed accessible with some know-how of computer hacking and a few tricks, and all without having to hire overpriced shady hackers who you may not always trust with your data. So, whether it be your child, employee, or possibly cheating spouse, you can now learn how to hack a computer remotely using these 3 simple methods illustrated below!
How to Remotely Access Another Computer without Permission?
Without having the correct login username and password credentials, it is incredibly difficult and also not ethical to remote access to computer on your own without any information, authentication, or validation given by the original user.
However, if you really need to hack into a computer from your computer for any safety reason. you will need to install a PC hacker in advance whenever you have the access to the target computer.
Is Remote Computer Hacking Possible?
Although not necessarily easy, remote hacking is definitely possible with the right techniques. To break into someone's computer system, you must gain the permission to do so, and it is important they do not realize that they have given it to you.
You will need to either know how to use some techniques or utilize some PC hackers. Now we are going to introduce 3 different ways to hack into someone's computer.

Way 1 - How to Remotely Hack Into a Computer with MoniVisor - 100% Safe & Stealth
Suitable for: For individuals or small teams with no need for technical expertise
Ease of Use: Easy
Rate:
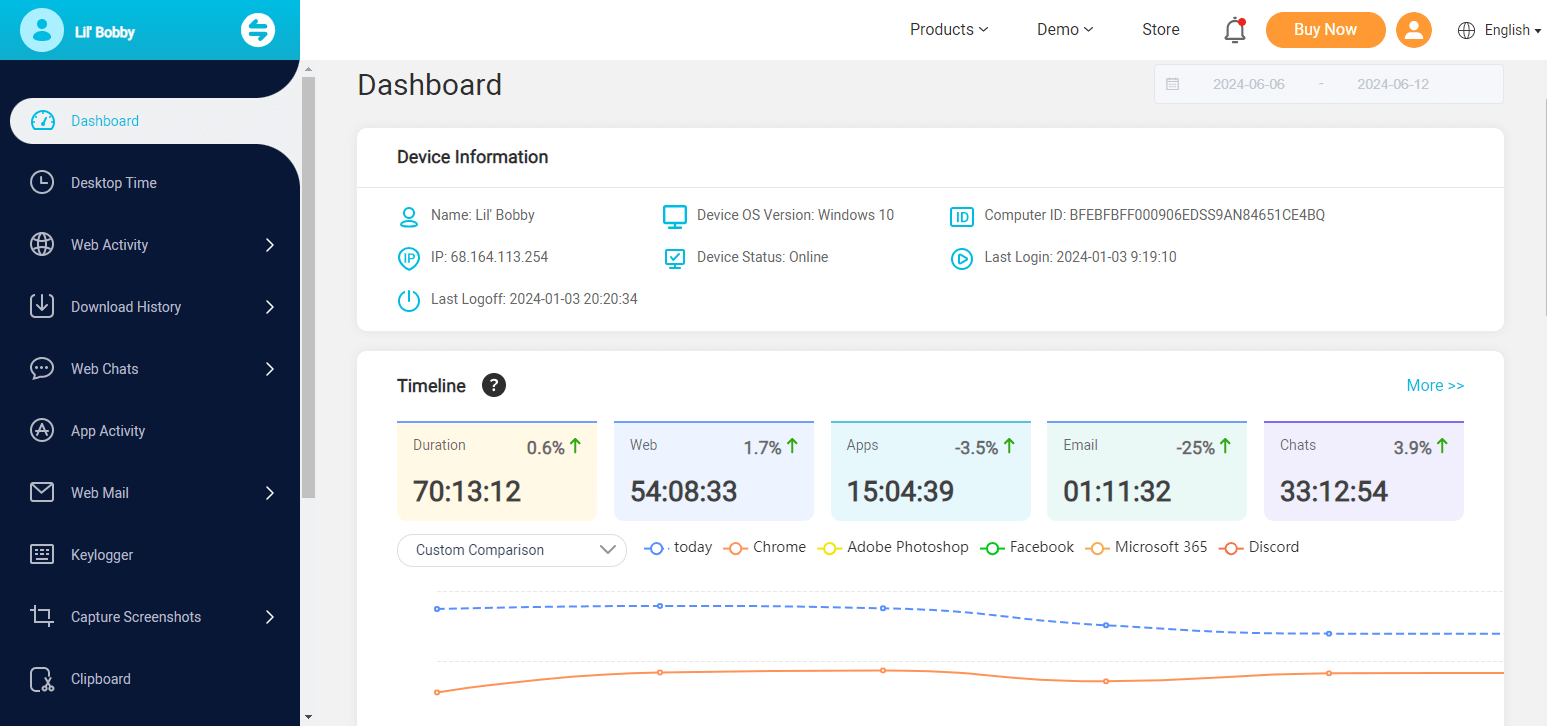
Ever thought about how your child or subordinates use the computers while you are away? No more as MoniVisor monitoring software is the perfect solution for that. You can use it to control another computer remotely. It records all activities on the target device, such as keystroke logging, social media monitoring, all web emails, and so on. Displaying the data in a well-organized beautiful layout on the online dashboard.
The installation and configuration process is seamless and convenient and you can start monitoring activity from your dashboard right away!
What makes this solution unique from others is that it does all this while remaining invisible on the target computer, meaning that the target will never know they have been hacked!
What You Can Do to Hack a Computer with Monivisor
As a professional computer monitoring program on Windows, MoniVisor can do computer hacks in terms of all kinds of different data and occasions. Let's check below!
Email monitoring: You could view all details of the emails received or sent on the computer. For example, Gmail, Outlook, Yahoo.
Browser activity: You are allowed to check the computer's browsing history to see what the person has been searching.
Social media apps monitoring: If the person logs into a social media account on broswer like WhatsApp, Facebook, Twitter, Instagram or Skype, you can see the chats secretly.
Screenshot capturing: This app can automatically take screenshots of the monitored PC while using, and the screenshot of the computer will sync to your online dashboard.
How to Hack into Someone's Computer without Login Credentials
Step 1: Get a valid account and license
In the beginning, you can click the button below to get a MoniVisor account by using a valid email address. Then get a plan according to your need. This is necessary for you to access the computer's data and enjoy all the features.
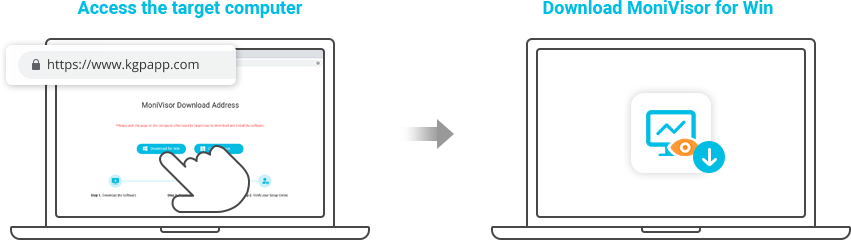
Step 2: Check the Setup Guide to download and install the app to target's computer.
This process may cost about 5 minutes to finish. There will be a clear guide for you. You will never have to worry about if the operation is difficult or not.
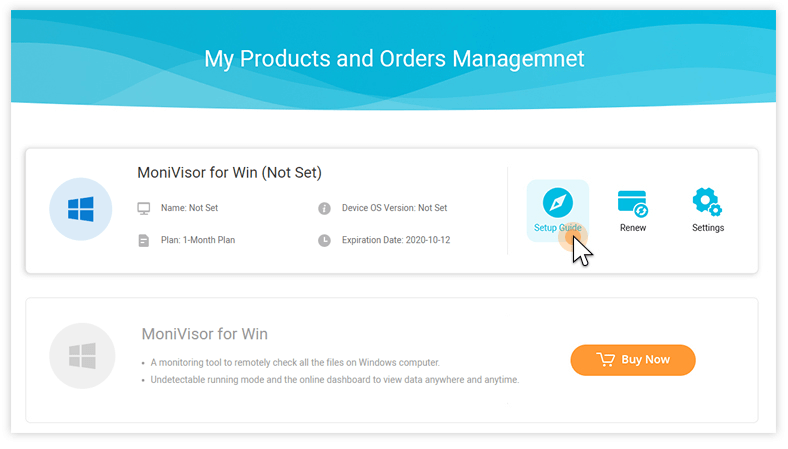
After the purchase, you will be led to the My Products page, here you can check the Setup Guide. When you have already successfully installed and activated the software, then you can log into the account on your own computer.
Step 3: Login to the online dashboard to hack a computer
Now, you have already finished the configuration. All you need to do is to view all the data and files from the target computer. Then you have hacked into someone's computer successfully.
If you are searching "how to hack into someone's computer without them knowing", this is an easy-to-use PC hacker and requires no preset of skill for its operation.
Also, the software running in the background will not cause the system to run slower and make the performance drop on the target computer. The name will not appear on the desktop and taskbar.
After reading the introduction and the steps on how to hack someone's computer with MoniVisor, we can know that this is an App suitable for everyone.
Indeed, there are other 2 ways to hack a computer without the help of such kind of professional software, but you have to be equipped with a good basis of technology. Check out the following two computer hacking skills.
Way 2 - Way 2 - Take Control of Someone's Computer via TeamViewer - Visible to the Target
Suitable for: Who knows the TeamViewer ID and password of the target computer.
Ease fo Use: Normal
Rate:
Another way you can do hacking computer is by installing or getting the users to install TeamViewer software.
This software enables you to literally take over a computer and control it from your device which is acting as a remote control, giving you access to all the data on the target computer.
How to hack a computer remotely by TeamViewer:
Download the TeamViewer on both computers.
Setup both computers to get ready for remote control.
Enter the username and password from the target device onto your computer in order to pair them.
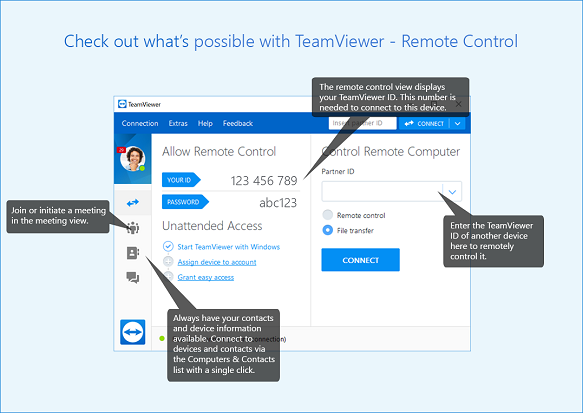
All this comes free of cost for a personal license, making this a great option for hacking into a computer.
This method, however, can prove to backfire if the user catches onto what is happening, as the software is clearly visible on the target computer, they can clearly know what are you doing if the screen is not locked.
You also need to have the same version and a stable and fast connection on both sides in order for this method to work effectively, a stable internet connection is not possible all the time making hacking and monitoring limited to only when the target computer is connected to LAN or Wi-Fi.
Way 3 - Bypass the Login Process on Windows - Difficult
Suitable for: Who knows a lot about computer technology and has much time to access the computer for setup.
Operation Difficulty: Super Hard
Rate:
While it is very tricky to bypass the Windows login process, it is definitely possible with the combination of Windows installation drive and Commands prompt, you can set up a new administrator account that has access to all data on the main account.
Note that this will not change the password that the main account uses, but you should be able to access, edit, and copy virtually anything from the main account.
How to hack into a PC by bypassing the login
Step 1: For this method, you need to first create a Windows installation tool on a USB with a minimum of 8 GB free storage. Then there are several small steps you need to do.
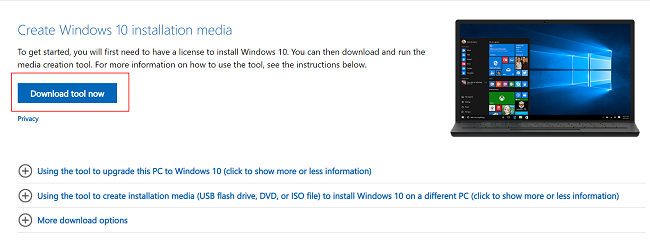
Attach the flash drive to your computer and open the Windows download page.
Click the "Download tool now", and then double click the tool after successful downloading.
Then follow the on-screen instructions to make sure to use your flash drive as the installation location.
Now leave the flash drive plugged in after the creation process completes.
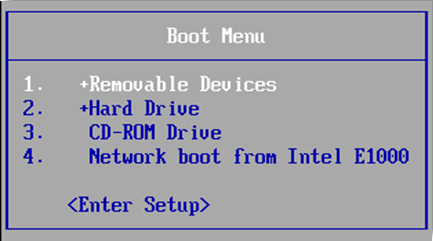
Step 2: Prompt your computer to start from the flash drive rather than the hard drive. Here you need to change your boot order and this needs you to access the computer's BIOS.
How to Enter BIOS?
First, you need to restart the computer.
Then wait for the computer's first startup screen to appear.
Press and hold Del or F2/F8/F12/ESC to enter setup.
Wait for your BIOS to load. This may take a few minutes then you can go to the BIOS settings menu.

Step 3: Now find the "Boot Order" section in the Boot or Advanced tab. Then select your flash drive's name, then press + until the flash drive is at the top of the list.
Step 4: On the setup screen, press Shift+F10 to open Command Prompt.
Step 5: After that, you need to replace the utility manager with Command Prompt which will then allow you to create a new administrator. By replacing Utility Manager with Command Prompt, you'll be able to execute administrator-level functions without having to log in.
Type move c:\windows\system32\utilman.exe c:\windows\system32\utilman.exe.bak into Command Prompt.
Press Enter
Type copy c:\windows\system32\cmd.exe c:\windows\system32\utilman.exe into Command Prompt.
Press Enter
Step 6: The last step is to Restart the computer and use the account you created to login in.
In order to successfully pull off this hack, it is necessary to have physical access to the target computer, and the setup process will take much time and the process is super technical for ordinary people.
Final Words
From now, you have learned how to hack a computer. However, we strictly discourage hacking for illegal purposes. Computer hacking should be used for ethical purposes such as parental control and supervising your employees at work, using these softwares and hacks for criminal activity may come with serious legal consequences however hence, it is very important to use these tools and hacks with utmost responsibility and care.
Out of all the ways, in our experience we found the MoniVisor for Windows turns out to be the best spy software for PC, even though it is a paid software, it being invisible in the target computer makes it the best way on our list as you can sneakily hack into the computer without the user ever finding out about it, making it ideal for those sneaky hacking scenarios.





