ClevGuard Support: Monitor Devices with Others' Permission.
Have you ever resorted to stealth monitoring to figure out what your employees are doing? This proactive approach serves a dual purpose: safeguarding individuals from potential threats and enhancing control over work time and productivity.
How do you achieve this level of oversight? Through the use of stealth viewer software. In this article, we will delve into the concept of stealth tracking, its legality, and one of the best hidden remote access software currently available in the market.
Definition of Stealth Monitoring
Stealth monitoring entails the deployment of specialized software designed to gather information about a user's computer activity covertly, without their explicit knowledge or consent. Unlike malicious entities such as malware or spy software that operate surreptitiously and harmfully, stealth viewer software is intentionally installed with the awareness and approval of an administrator.

This technology enables employers to monitor various aspects of computer usage, including tracking visited websites, monitoring communications with others, and even capturing screenshots of the user's desktop for comprehensive oversight.
Stealth Tracking, Legal or Not?
The legality of stealth tracking hinges significantly on the jurisdiction and the intended purpose of the software. In numerous countries, employers possess the legal right to monitor their employees' computer activities during work hours, provided it aligns with specified objectives like quality control, property preservation, and data security. However, employers must observe certain conditions, such as restricting the use of the software to work hours and company-owned equipment.
In personal contexts, installing hidden remote access software on someone else's computer without their knowledge or consent is typically deemed illegal. Respecting privacy rights is paramount, and obtaining proper authorization before monitoring another individual's computer activity is a crucial legal and ethical consideration.
What Is Stealth Employee Monitoring Software
Stealth employee monitoring software is intricately crafted to discreetly observe and track the computer activity of employees. Once this type of software installed on the end device, it goes hidden. No icon or notification on the desktop or menu bar.
This specialized tool allows employers to monitor how employees utilize their work computers, ensuring adherence to company policies and appropriate use of company resources.
Best Stealth Viewer Software
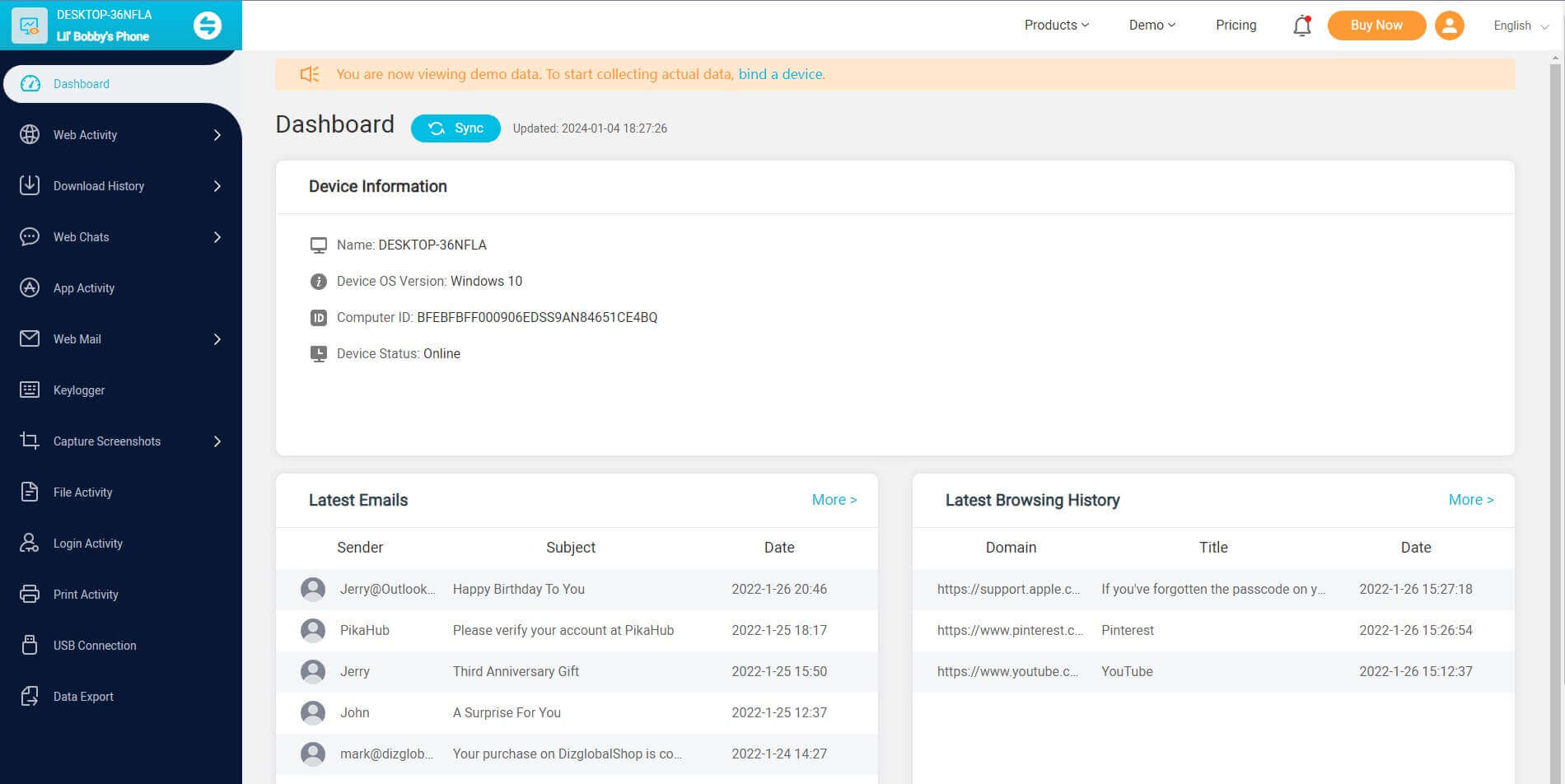
When it comes to the stealth viewer software, MoniVisor stands out as a highly recommended solution. This powerful hidden remote access software offers comprehensive monitoring and control features for both employers and parents. Let's delve into some of its key features:
MoniVisor: Hidden remote access software
MoniVisor may not be the biggest name in this industry, its functionality secures the place of the best Windows hidden remote desktop software in 2024. Being stealth means completely disappeared from the screen. After the program is downloaded, it goes hidden and nobody can detect it, even from the start menu, desktop, task bar, Task Manager, and Windows Control Panel. It records every data you need secretly. Isn’t fantastic? Have a glimpse of what it offers for employers:
-
View exchanged emails: MoniVisor is able to access and obtain the content of sent and received emails, including the text, images, attachments, and other details. In workplaces, email monitoring helps enforce company policies, enhance security, and prevent unauthorized or inappropriate communication.
-
Check file activity: This hidden remote access software can review and monitor the file interactions, downloads, modifications, or access made to files on a computer system or network. Besides, file folder changes can be recorded as well. This process is often carried out for various purposes, including cybersecurity, system administration, or compliance monitoring.
-
Track software usage: Another features by MoniVisor is to track the software usage. It monitors and records how applications or software programs are utilized on a computer or network. By providing the time usage, this process provides insights into how employees, users, or systems interact with software applications.
-
Record keystroke inputs: If you need a Windows-based keylogger, MoniVisor won’t let you down. It captures and logs the individual keystrokes made by a user on a computer or keyboard. Employers may use keylogging programs to monitor employee activities and ensure that employees are using company resources appropriately on company-owned computers.
-
Monitor real-time desktop screen: MoniVisor provides the capability to view and control the remote user's desktop in real-time. This feature is invaluable for employers seeking to monitor employee activities and ensure task focus. Additionally, parents can use this functionality to oversee their children's online activities, promoting a safer online environment.
I bet the abovementioned features can help you gain a whole picture of what MoniVisor is. Unlike some stealth viewer software, this one has an easier installation process and an intuitive online dashboard. That is to say, it will save you troubles from software configuration. If you still have any doubt towards this program, check the Free Demo to see whether this software can fulfill all your needs.
How to configure stealth monitoring on PCs:
- Step 1: Place a suitable order and create an account to activate all the features of MoniVisor.
- Step 2: Access the MoniVisor’s download package at the target PC from the give address: www.installapp.net. The software goes incognito upon installation.
- Step 3: Navigate to the online dashboard and login to your personal account on your end. Seconds later, you can see all the synced data. What needs attention is that the first-time syncing takes a longer time than usual. Once the target computer is on, you can check the computer activities in stealth mode.
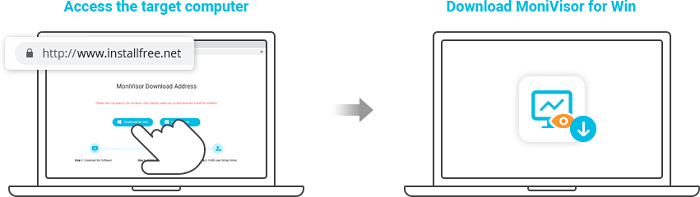
You need to install the stealth viewer software on the target computer and access the online control panel at your end. This is how the PC monitoring works.
Wrapping Up
Stealth employee monitoring software, such as MoniVisor, provides employers with a powerful tool to monitor computer activities discreetly. With the right hidden remote access software, you can have peace of mind knowing that you have the necessary visibility and control over computer activities. Why wait? Seize the benefits of stealth tracking and effortlessly monitor computer activities for enhanced oversight and efficiency.





